AI has been thrown at a range of problems, and recently several platforms have appeared allowing keywords to create images. It’s amazing, game changing, and highly frustrating.
Why game changing? Well immediately, I as an artistically unskilled Luddite could create images that otherwise are totally beyond my ability to create. Sure I could hire an artist, give them guidance, and iterate through concepts till I saw what I wanted – this does that in a more obtuse way – without the artist. All I need is a Midjourney (MJ) subscription, patience, and the time it takes to ponder which keywords and options might create what I’m looking for. Often MJ created attractive imaged which are “wrong”, and that’s really my issue for not knowing what words the AI needs to create what I want – not unlike miscommunication with a designer or artist.
The key point – midjourney allows somebody to look at options but not control the process. If you have an exact image in mind then hire an artist, because MJ won’t help you. If you want to iterate through strange and random art till you are frustrated or find what you want, then MJ is for you. Your call.
Are these “works of art”? No, not really. You as the keyword suppler need to have an intent to create, and a knack to finding the right terminology to drive the AI toward the images you want. Anything is art, but I feel generating images this way is not as skillful or purposeful as the processes an artist uses to create an image. This is discovery through randomisation, not discovery through artistic creative process (or that could be too snobby, but you get the difference).
Does AI Art have a place? Hell yes – as a way to iterate, discover, create, and challenge a concept it is very effective and useful. Images are created in minutes, and can be created in the background while you do other things. I re-watched a favourite film while creating concepts, and it was a night well spent.
For example – trying to create an image of a sea monster rising out of the ocean…has given me a challenge. Below is an image gallery of the attempts to create this – and I don’t have anything I like at all yet…
I will continue, and have the benefits of no deadline, no budget, and a nagging urge to prove I can do it. I hope you get to experiment with an AI Art tool once or twice.
 RSS Feed
RSS Feed


























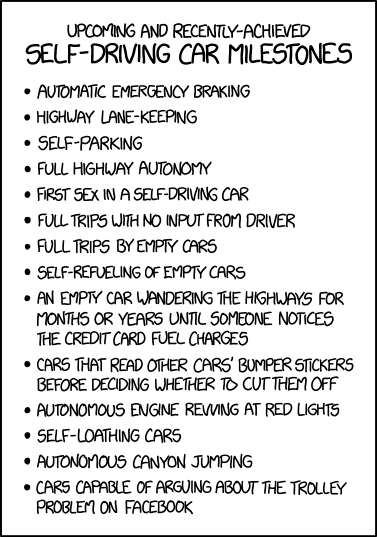 Great comic as usual. Its only as the concepts drift wistfully past your personal point of insanity that it makes you think something here might be unreasonable. Should the AI decide that mimicing driver behaviour is better than efficiency; then we are all doomed.
Great comic as usual. Its only as the concepts drift wistfully past your personal point of insanity that it makes you think something here might be unreasonable. Should the AI decide that mimicing driver behaviour is better than efficiency; then we are all doomed.